When you or I send something to the cloud, where does it go? Do you know? Does anyone know? Questions like these have been cropping up left and right, and with companies from Apple to Microsoft moving to the cloud, they are bound to get more common. As with most new technologies, the media has done a great job trying to scare people without providing very many explanations, and with all the recent news of large companies getting hacked, there must be something to their claims that the cloud is a big, scary, unsecured place, right? Well, about that…
Before we get too deep into things, let’s look back and see if we can’t pin down exactly what the cloud is. At it’s most basic, cloud computing is simply letting a server somewhere out in the depths of the internet do the things that would normally be taken care of by components inside your local computer. Whether it’s storing files or processing data, cloud computing is the digital equivalent of outsourcing, letting far-away servers do your machines work cheaper and more efficiently than your computer could do it on it’s own. The idea behind cloud computing goes all the way back to the beginning of computing. In those dark ages, massive supercomputers were the standard, and in an effort to allow multiple people to use one mainframe simultaneously, they would often be fitted with remote “terminals” which functioned as essentially a monitor and keyboard, and let the mainframe do all the work.
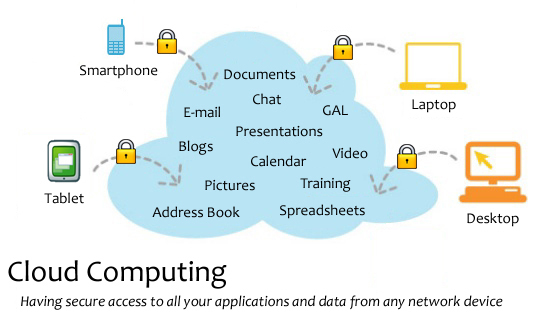
Flash forward a couple of decades to the introduction of popular free email services like AOL and Yahoo and Hotmail. Almost since these services came into being, people realized that instead of saving documents to cumbersome disks, they could simply email the files to themselves and pull them up later whenever they needed them. As Google introduced near-unlimited email storage, this practice only became more widespread. Now, as the internet has grown to be all-encompassing, almost any function or application can be used in a cloud version, allowing you to access data and programs you need from anywhere you can find a wi-fi signal.
So the big question is: Is it safe? Shockingly, and despite what late-night news anchors and screaming headlines have to say, yes. Or at least safer than the alternative. The most common argument against cloud computing I see is “Well, I don’t trust having my data floating out there in the ether.” That could be a valid argument, until you begin to realize that your data is far safer on these large corporate cloud servers than it could possibly be in your possession. After all, look at the numbers: The vast majority of identity theft happens not from compromised corporate servers but from common theft of wallets, ‘phishing’ attacks that get you to voluntarily hand over info to an attacker, and simple lost documents and credit cards. Not enough for you? Consider this, then: Over 1/4th of all computers connected to the internet are part of a botnet! Chances are quite good that your machine is compromised. If not yours, than one of your friends’ definitely is. So here’s the million dollar question: who do you trust more to secure your data? You with your outdated copy of Norton or a corporate server farm that pays some very smart people a lot of money to make sure their data is safe? And granted, occasionally a story about a large hacking hits the news, as with the PS3 network recently, but you have to consider that less computers were compromised in that massive attack than get attacked and attached to bot-nets (for the less tech-savvy, a bot-net is a network of computers with hidden malicious code that can be activated remotely for purposes that include spamming and denial of service attacks against websites and companies) daily. We just don’t hear about the hundreds of millions of individual users because, well, they aren’t Sony.
The bottom line is that while putting your data in the cloud is entirely a personal choice (for now), you should make that choice with all the facts arrayed in front of you. There is absolutely nothing that a large server could do with your data that you, or someone who uses your computer, or a pickpocket, couldn’t do a lot easier and more efficiently. Here’s a metaphor to close us out and take us home: Think of computers as houses. You could go and build your house out in the middle of the woods, far away from prying eyes and nosy neighbors, but by doing so you raise the risk that someone can break in, take your stuff, make themselves at home, and generally make your life miserable while you are far from civilization and help. Or you could build your house in the walled city of a cloud computing server. Sure, your neighbors might be able to hear you through the walls, and maybe people on the street can see through your windows, but on the other hand, you’ve got a big wall and a fleet of police officers in case anything goes wrong. Think about it.
